Table of Contents
- What OFAC Hiring Compliance Means for Remote-First Companies
- Why Hiring a Sanctioned Worker Triggers OFAC Violations
- OFAC Penalties: What Companies Actually Face
- The Laptop Farm Playbook: How Sanctions Evasion Works in Hiring
- Where Traditional Background Checks Fail Against Sanctions Fraud
- Deepfake Detection as a Sanctions Compliance Layer
- How Tofu Provides OFAC Compliance for Hiring Processes
- The North Korean IT Worker Threat: Real Cases from 2025 and 2026
- Final Thoughts on OFAC Compliance in Distributed Hiring
- FAQs
TLDR:
- OFAC hiring compliance operates under strict liability: processing even one paycheck for a sanctioned worker triggers violations up to $368,136 per transaction, regardless of intent. Background checks verify the identity exists and clears the SDN list but can't verify the person behind the camera actually owns that identity.
- Two U.S. nationals received prison sentences of 108 and 92 months in April 2026 for placing North Korean IT workers at more than 100 American companies using stolen identities, laptop farms, and VPN tunneling. The defrauded companies ran background checks and video interviews. The compliance gap wasn't screening credentials, it was verifying the human behind them.
- Traditional background checks miss sanctions fraud because they run applicant-by-applicant in isolation with no location verification, no resume metadata analysis, and no cross-applicant fraud ring detection. Deepfake tech now lets operatives wear stolen American faces on video calls after the SDN check already passed.
- Real-time deepfake detection closes the compliance gap by analyzing biometric inconsistencies during interviews: lip sync, eye movement, facial construction, voice patterns. It flags synthetic video, cloned audio, and identity mismatches before a hire decision becomes an OFAC violation.
The background check cleared. The resume matched a real American identity. The video interview looked normal. But if that candidate was using deepfake tech to mask a sanctioned worker, you've already violated OFAC hiring compliance rules and exposed your company to civil penalties reaching $368,136 per transaction. Two U.S. nationals received prison sentences of 108 and 92 months in April 2026 for running a North Korean IT worker fraud scheme that placed operatives at more than 100 American companies. Standard verification confirmed every credential existed. What it couldn't catch was that the person behind the camera wasn't the person who owned them.
What OFAC Hiring Compliance Means for Remote-First Companies
For remote-first companies, OFAC hiring compliance goes beyond a legal checkbox. The Office of Foreign Assets Control prohibits U.S. employers from paying wages to sanctioned individuals, and violations carry civil penalties reaching $368,136 per transaction under strict liability, meaning intent doesn't matter. With fully distributed teams, the compliance challenge moves from verifying credentials to verifying the human behind them. Your background check confirms the identity exists and clears the SDN list. What it can't confirm is whether the person on your Zoom call actually owns that identity. When a North Korean operative applies using a stolen American SSN, every standard verification point passes cleanly. The laptop ships to a U.S. location. The video interview looks normal. And the moment you process that first paycheck, the violation has occurred.
The enforcement record here is not ambiguous. In one of the largest schemes charged by the Department of Justice, an Arizona woman was sentenced to 102 months in prison after helping North Korean IT workers land jobs at more than 300 U.S. companies. Prosecutors documented 68 stolen identities and 309 defrauded businesses tied to that single operation. April 2026 brought fresh sentences when two U.S. nationals received 108 and 92 months respectively for a scheme that compromised over 80 U.S. identities and placed fraudulent remote workers at more than 100 American companies. The companies defrauded weren't negligent in any obvious way. They ran background checks, reviewed resumes, and conducted video interviews. The problem was the identity they screened belonged to a real American, not the operative behind it. The DOJ's enforcement posture in 2025 and 2026 signals this is now a continuing priority, not a one-off sweep. Facilitators are being charged, and companies that processed payroll for these workers face OFAC scrutiny regardless of whether they knew.
Why Hiring a Sanctioned Worker Triggers OFAC Violations
Under the International Emergency Economic Powers Act (IEEPA), any transaction that transfers value to a Specially Designated National (SDN) is prohibited. Payroll qualifies. OFAC maintains a public SDN list of sanctioned individuals, entities, and countries, and compensating anyone on it constitutes a prohibited transaction regardless of how the payment is structured.
The part that catches most compliance teams off guard is the strict liability standard. OFAC does not require proof of intent to impose penalties. If you hired a sanctioned worker and processed even a single paycheck, the violation exists. Lack of knowledge factors into the severity of penalties, not whether a violation occurred.
OFAC Penalties: What Companies Actually Face
OFAC violations carry civil penalties up to $368,136 per transaction, and that ceiling rises with inflation adjustments each year. Willful violations can trigger criminal fines up to $1 million per count, plus imprisonment. The enforcement record shows OFAC doesn't wait for egregious cases to act. In 2019, they imposed a $75,375 penalty on a California company that processed payments for a single sanctioned individual over 18 months. The violation counted per paycheck, not per hire. For companies that unknowingly hired a sanctioned individual, "we didn't know" rarely works as defense. OFAC operates under strict liability for many violations, meaning intent doesn't factor into whether a penalty applies. What does factor in is whether you had a compliance program designed to catch this before payroll processed. The companies facing DOJ charges for North Korean IT worker schemes all had background checks in place. What they didn't have was verification that the person behind the credentials matched the identity being screened.
The Laptop Farm Playbook: How Sanctions Evasion Works in Hiring
The playbook is methodical. A North Korean operative applies under a stolen American identity: real SSN, fabricated employment history, plausible social profiles built to pass SDN screening. A U.S.-based facilitator receives the company laptop at a domestic location, creating the appearance of domestic employment. Remote access software then tunnels that device overseas, where the actual worker operates behind layers of VPN routing that mask the foreign IP throughout. The wages route through intermediary accounts before reaching handlers in Pyongyang. The companies defrauded in the Arizona and 2026 DOJ cases weren't negligent. They ran background checks, verified employment history, and conducted video interviews. What they couldn't verify was whether the person behind the camera actually owned the identity being screened, and that gap is where the violation occurred.
Standard background checks confirm the identity exists and clears the SDN list. They don't verify that the person on your video call actually holds that identity. The name passes. The person behind it never will.
Where Traditional Background Checks Fail Against Sanctions Fraud
The SDN list check flags sanctioned names. What it can't detect is that a stolen American identity has been layered over a North Korean operative to pass that check cleanly. That's a different problem entirely, and background verification vendors weren't built to solve it.
Location verification doesn't exist in standard background check workflows. Resume metadata analysis, which can surface connections between fraud ring applicants through shared file authorship and creation timestamps, never happens. And because checks run applicant-by-applicant in isolation, no one catches when multiple submissions share suspicious IP clusters, device fingerprints, or document templates across companies.
Each gap alone is a problem. Together, they're a compliance hole the size of a laptop farm.
Verification Layer | What Traditional Background Checks Catch | What They Miss in Sanctions Fraud |
|---|---|---|
Identity Verification | Confirms the identity exists in government databases, SSN is valid, name matches official records | Cannot verify the person submitting the application actually owns that identity. Stolen American credentials pass cleanly because the underlying identity is legitimate. |
SDN List Screening | Flags exact name matches against OFAC's Specially Designated Nationals list | Sanctioned operatives using stolen U.S. identities never appear on the list under those names. The check passes because it's screening the victim's identity, not the fraudster's. |
Employment History | Verifies past job titles and dates of employment with listed employers | Fabricated work histories with real company names pass when references are coordinated. No mechanism to detect resume metadata, shared file authorship, or fraud ring patterns across applicants. |
Location Verification | Standard background checks do not include location verification in their workflow | No detection of VPN tunneling, IP masking, or laptop farms where U.S.-based facilitators receive hardware that's remotely accessed from sanctioned countries. |
Video Interview Validation | Background checks occur before interviews and do not monitor live video interactions | No capability to detect deepfake video, AI-generated faces, voice cloning, or proxy swapping during interviews. The person on camera may not be the person who applied. |
Cross-Applicant Analysis | Each background check runs in isolation on a single applicant | Cannot identify when multiple applications share suspicious IP clusters, device fingerprints, document templates, or metadata signatures indicating coordinated fraud rings. |
Deepfake Detection as a Sanctions Compliance Layer
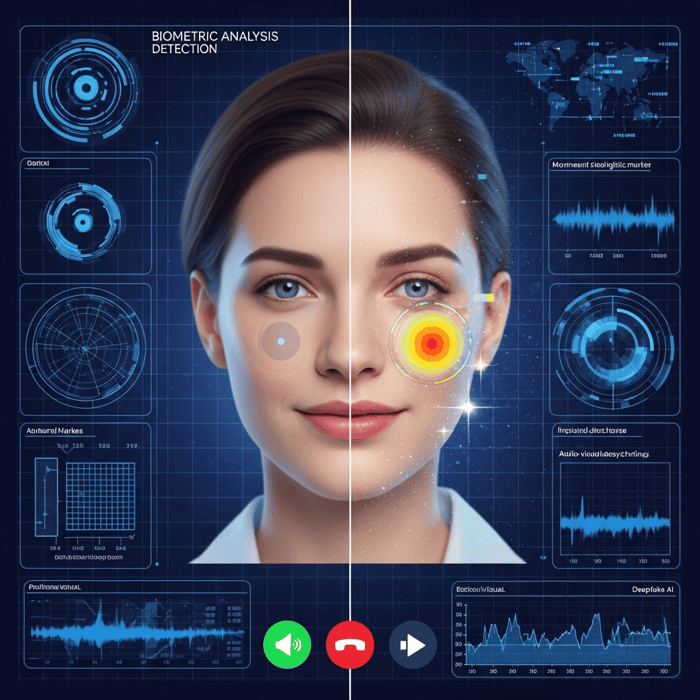
Video interviews became the last line of defense. Deepfakes made them a liability.
An operative with a stolen American identity doesn't need to be physically present. AI-generated video lets them wear someone else's face on a Zoom call after the SDN list and background check already passed. The interview was the only remaining catch point, and now that's compromised.
Real-time deepfake detection closes that gap by analyzing biometric inconsistencies during the interview itself, flagging anomalies before a hire decision is made and before a sanctions violation occurs.
How Tofu Provides OFAC Compliance for Hiring Processes
Tofu's deepfake detection sits directly inside the hiring workflow, flagging synthetic video, cloned audio, and identity mismatches before a candidate ever reaches an offer. When a screened applicant triggers a sanctions match, that signal routes immediately to compliance review. No manual cross-referencing against OFAC's SDN list. No gap between detection and escalation.
The North Korean IT Worker Threat: Real Cases from 2025 and 2026
The Arizona woman sentenced to 102 months in prison for running a North Korean IT worker scheme wasn't an isolated case. She helped place operatives at more than 300 U.S. companies using 68 stolen identities, and prosecutors documented how each placement followed the same pattern: stolen American credentials, fabricated work histories, and remote access tunneling that made domestic hiring look legitimate. The two U.S. nationals sentenced in April 2026 to 108 and 92 months ran a parallel operation that compromised over 80 identities and placed fraudulent workers at more than 100 companies. What connects these cases isn't the scale. It's that the defrauded companies weren't negligent. They ran background checks, verified employment history, and conducted video interviews. The compliance gap wasn't in screening the identity; it was in verifying the person behind it actually owned that identity.
Why Hiring Is the Vulnerability
Video interviews are no longer proof of identity. Deepfake tech lets a single handler run multiple candidate personas across simultaneous interviews, with face and voice swapped in real time. By the time a background check clears on a synthetic identity, the worker is already onboarded and inside your systems.
Final Thoughts on OFAC Compliance in Distributed Hiring
The companies facing DOJ charges in 2025 and 2026 for hiring North Korean IT workers all had one thing in common: they screened the identity, not the person. OFAC hiring compliance built on background checks alone assumes the two are the same, and that assumption is now a liability. Real-time deepfake detection and fraud network intelligence verify the human behind the credentials before the hire becomes a violation. If you're building compliance for a remote-first team and want to see what that looks like in practice, let's talk.