Table of Contents
- Types of Resume and Application Fraud Targeting Recruiters
- Red Flags in Resume Content and Formatting
- Red Flags During Application Submission
- Red Flags During Video and Phone Interviews
- Resume Metadata and Document Analysis
- Verifying Employment History and Credentials
- Cross-Referencing Social and Professional Profiles
- State-Sponsored IT Worker Fraud and DPRK Schemes
- Building Fraud Detection Into Your Hiring Process
- Automated Fraud Detection and AI Screening Tools
- Final Thoughts on Catching Resume and Application Fraud
- FAQs
Sixty to seventy percent of people admit to lying on a resume at least once. The bigger problem is the quarter of candidate profiles that Gartner says will be entirely fake by 2028. How to review resumes for fraud isn't about catching job title embellishment anymore. It's about spotting synthetic identities, AI-generated applications, proxy interviewers, and state-sponsored IT workers.
TLDR:
- Recruiters face synthetic identities, deepfakes, and state-sponsored IT worker fraud beyond embellishment.
- Resume metadata, IP logs, and social profile age reveal fraud before any human review happens.
- Deepfakes and proxy interviewers appear in 18% of video interviews, per 2025 Greenhouse data.
- Manual verification catches some fraud but misses patterns across hundreds of applications at scale.
- Tofu's FraudDetect screens applicants across 40+ signals at submission with 97% accuracy.
Types of Resume and Application Fraud Targeting Recruiters
Resume fraud isn't new, but the version recruiters face in 2026 looks nothing like what HR teams dealt with a decade ago. Here's what recruiters are up against right now:
- Traditional embellishment: fabricated credentials, inflated titles, falsified employment dates
- AI-generated applications: bulk-generated resumes optimized to pass ATS filters
- Synthetic identities: real employment histories stitched with false contact details and fabricated personal data
- Deepfake interviews: AI-generated video and audio used to impersonate candidates during live calls
- Proxy interviewers: stand-ins hired to pass technical screens, replaced by the unqualified hire on day one
- State-sponsored IT worker fraud: foreign threat actors using stolen identities and VPNs to infiltrate remote technical roles
Embellishment wastes time but synthetic identities open the door to insider threats like State-sponsored schemes which can trigger OFAC violations.
Red Flags in Resume Content and Formatting
AI-generated resumes are the easiest to spot. The language is polished but hollow: bullets mirror the job description almost word-for-word.
Content Red Flags
- Bullet points that lift exact phrases from your job posting
- Generic achievements with suspiciously round numbers ("increased revenue by 200%")
- Job titles that escalate too fast without supporting context
- Employment gaps filled with vague consulting or freelance descriptions
Formatting Red Flags
- Dates that align perfectly but leave no room for transitions between roles
- Roles with identical tenure lengths across multiple jobs
- Contact details that don't match the listed location
Fraud rings often recycle resume templates, so near-identical formatting across separate applications is rarely a coincidence.
Red Flags During Application Submission
Before a recruiter ever opens a file, the submission itself carries signals. Email accounts created days before applying, VOIP numbers with no traceable carrier history, IP logs routing through known proxy servers: the application metadata is what you should check first.
Red Flags During Video and Phone Interviews
As of 2025, 18% of hiring managers caught deepfakes in video interviews and that's only the ones they noticed.
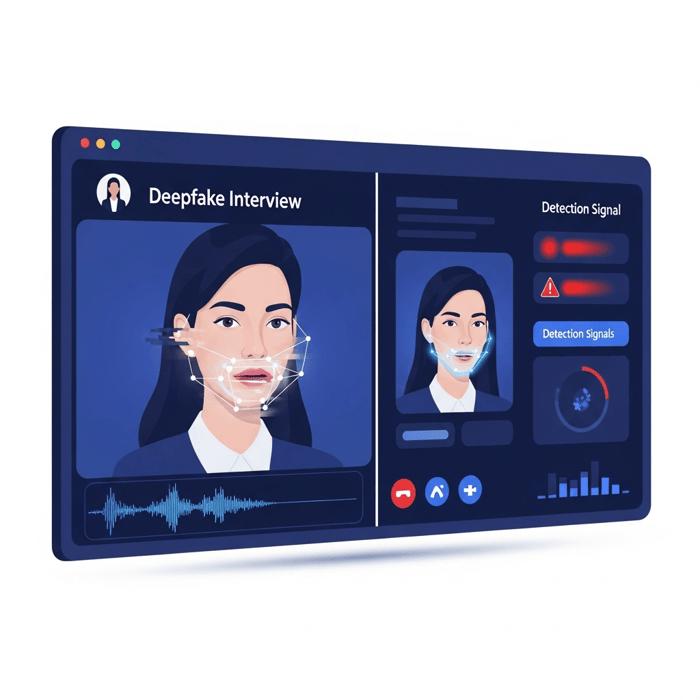
Visual and Audio Artifacts
- Lip movement that doesn't sync cleanly with speech
- Unnatural facial edges or slight blurring around the jawline
- Voice that sounds processed or slightly delayed from mouth movement
- Lighting that feels inconsistent with the stated location
Behavioral Tells
- Scripted, overly polished answers to open-ended questions
- Long pauses before follow-ups, as if waiting for a prompt
- Inability to elaborate when asked to walk through a specific decision
- Evasiveness about tools, teammates, or environments from past roles
Inconsistencies Across Stages
A candidate who aced the technical screen but stumbles through basic questions in a final round may not be the same person. Watch for changes in communication style, accent, or vocabulary between calls.
Resume Metadata and Document Analysis
The resume you read and the file you receive are two different documents. One tells you what a candidate wants you to know. The other tells you what they didn't think to hide.
Every resume file carries embedded metadata: creation date, last-modified timestamp, authorship name, editing software, and in many cases, geographic indicators tied to the machine that built it. A file created at 3 a.m. in a timezone six hours ahead of the candidate's listed location is worth a second look. An "author" field populated with a name that doesn't match the applicant is a harder flag to explain away.
Fraud rings run on templates. When multiple applicants submit files with identical formatting structures, the same authorship field, or sequential creation timestamps, that's a production line. Metadata analysis catches the pattern across the whole pool.
A few specific signals worth checking:
- Creation and modification dates that don't align with claimed job history timelines
- Authorship fields with names that differ from the applicant's stated identity
- Editing software inconsistent with the candidate's claimed technical background
- Template signatures or style identifiers shared across applications to the same role
- Geographic metadata suggesting the file was created in a location the candidate never mentioned
Pulling metadata from every submitted file and comparing file fingerprints across hundreds of applications isn't something a recruiter has time to do. That trail is worth following.
Verifying Employment History and Credentials
Building a Verification Routine That Scales
A repeatable checklist applied consistently across finalists is faster than ad hoc digging and harder to game.
For employment history:
- Call the company's main HR line directly, not the number the candidate provides, since fraudulent applicants frequently list personal contacts who pose as former employers.
- Confirm job title, tenure, and eligibility for rehire, as discrepancies in any of these are red flags worth pausing on.
- Ask whether the manager listed as a reference actually worked there during the candidate's stated tenure.
Spotting Fake References
The tells are subtle:
- Reference phone numbers that go straight to voicemail with generic greetings instead of a person or company name.
- Email accounts on free domains instead of verified company domains.
- References who can confirm every detail but cannot recall a single specific project, challenge, or outcome.
When a reference is suspiciously available, immediately responsive, and perfectly complementary, treat that as a signal.
Cross-Referencing Social and Professional Profiles
Account age is the fastest signal. A profile created two weeks before the application date, with 47 connections and no activity history, is a prop. Genuine accounts accumulate over years.
What to Check on LinkedIn
- Account creation date relative to application date
- Whether listed employers have company pages and whether the candidate appears in their employee network
- Endorsement patterns, since real skills have endorsements from varied, real people
- Whether the profile picture reverse-searches to a stock image or someone else entirely
GitHub and Technical Profile Verification
For engineering roles, GitHub history is harder to fake. Look at contribution cadence, commit quality, and whether the repositories reflect the claimed experience level. A senior engineer with three public repos all created last month is worth questioning directly.
State-Sponsored IT Worker Fraud and DPRK Schemes
According to the U.S. Department of the Treasury, DPRK IT worker schemes generated $800 million in 2024 alone, with proceeds flowing directly to North Korea's weapons programs. Hiring one isn't a bad hire. It's a potential OFAC violation.
Building Fraud Detection Into Your Hiring Process
Stage-by-Stage Fraud Checks
- Application submission: metadata review, IP and device analysis, email and phone verification
- Resume review: content and formatting red flags, employment timeline consistency, social profile cross-reference
- Phone/video screen: identity consistency checks, behavioral observation
- Technical interview: compare communication style and ability against earlier stages
- References and credentials: direct verification with HR departments and registrars
When to Escalate
Not every flag warrants rejection. Set a clear threshold: one soft signal gets noted, two or more hard signals get escalated. Document every escalation so patterns across applicant pools become visible over time.
Hiring Stage | Primary Red Flags to Check | Verification Actions |
|---|---|---|
Application Submission | Email created days before applying, VOIP numbers with no carrier history, IP logs through known proxy servers, resume metadata showing authorship name mismatch, creation timestamps in unexpected timezones | Run metadata extraction on all resume files, cross-reference IP geolocation against stated location, verify email account age and domain authenticity, check phone number carrier type and registration date |
Resume Content Review | Bullet points lifting exact job posting phrases, suspiciously round achievement numbers, job title escalation without context, identical formatting across multiple applications, employment gaps filled with vague consulting descriptions | Compare resume language against job description for verbatim matching, verify employment timeline consistency, check for template signature patterns across applicant pool, flag dates with no transition room between roles |
Social Profile Cross-Reference | LinkedIn account created within two weeks of application, profile with under 50 connections and no activity history, profile picture reverse-searches to stock image, listed employer has no company page or candidate not in employee network | Document account creation date, verify employer company pages exist and candidate appears in network, check endorsement patterns for authenticity, run reverse image search on profile photos |
Phone and Video Interviews | Lip movement not syncing with speech, unnatural facial blurring around jawline, processed or delayed voice quality, scripted answers with long pauses before follow-ups, inability to elaborate on specific past decisions | Observe for visual and audio artifacts during live calls, ask open-ended questions requiring elaboration, request specific examples from claimed experience, compare communication style and vocabulary against earlier interactions |
Technical Assessments | Performance dramatically different from screening stage, communication style shift between interviews, GitHub account with three repos all created last month despite senior-level claims, contribution history inconsistent with experience level | Compare technical ability across multiple interview stages, review GitHub commit quality and contribution cadence, verify repositories reflect claimed expertise level, ask candidate to walk through specific code decisions |
Reference and Credential Verification | Reference phone goes straight to generic voicemail, email on free domain instead of company domain, reference cannot recall specific projects or outcomes, credentials from unaccredited institutions or registrars with no verification database | Call company main HR line directly, not the number the candidate provides, confirm job title and tenure and rehire eligibility, verify manager listed actually worked there during stated period, check credentials against official registrar databases |
Automated Fraud Detection and AI Screening Tools
Manual review catches some fraud. It misses most of it. Screening applicants for overlapping resumes, metadata, spoofed locations, and synthetic identities while running a full pipeline isn't feasible without automation.
Purpose-built tools close it. Tofu's FraudDetect screens every applicant across 40+ signals the moment they hit your ATS.
Final Thoughts on Catching Resume and Application Fraud
Most fraud gets filtered out when detection happens at submission, not during the interview stage. How to review resumes for fraud is less about recruiter training and more about automated checks running in the background before anyone opens a file. The volume problem is real, and manual verification doesn't keep pace with fraud rings that submit hundreds of applications a week. If you're seeing applicants that don't add up, reach out to our team and we'll walk through what we're catching. The right tooling stops fraud before it wastes your recruiters' time.